Introduction
Let's Encrypt is a Certificate Authority (CA) that provides an easy way to obtain and install free TLS/SSL certificates, thereby enabling encrypted HTTPS on web servers. It simplifies the process by providing a software client, Certbot, that attempts to automate most (if not all) of the required steps. Currently, the entire process of obtaining and installing a certificate is fully automated on both Apache and Nginx.
In this tutorial, you will use Certbot to obtain a free SSL certificate for Nginx on Ubuntu and set up your certificate to renew automatically.
Getting started
Installing Certbot
Certbot is in very active development, so the Certbot packages provided by Ubuntu tend to be outdated. However, the Certbot developers maintain a Ubuntu software repository with up-to-date versions, so we'll use that repository instead.
First, Add Certbot PPA::
sudo apt-get update sudo apt-get install software-properties-common sudo add-apt-repository universe sudo add-apt-repository ppa:certbot/certbot sudo apt-get update
Install Certbot:
Run this command on the command line on the machine to install Certbot.
sudo apt-get install certbot python-certbot-nginx
Certbot is now ready to use, but in order for it to configure SSL for Nginx, we need to verify some of Nginx's configuration.
Nginx's Configuration
Certbot needs to be able to find the correct server block in your Nginx configuration for it to be able to automatically configure SSL. Specifically, it does this by looking for a servername directive that matches the domain you request a certificate for.
Open the server block file for your domain using vim or your favorite text editor.
sudo vim /etc/nginx/sites-available/example.com
Find the existing server_name line. It should look like this:
. . . server_name example.com www.example.com; . . .
If it does, you can exit your editor and move on to the next step.
If it doesn't, update it to match. Then save the file, and quit your editor. In many cases it will appear like: example.com.conf.
Verify the syntax of your configuration edits: sudo nginx -t
If you get an error, reopen the server block file and check for any typos or missing characters. Once your configuration file's syntax is correct, reload Nginx to load the new configuration.
sudo systemctl reload nginx
Certbot can now find the correct server block and update it.
Next, we'll update our firewall to allow HTTPS traffic.
Allowing HTTPS Through the Firewall
If you have the ufw firewall enabled, you'll need to adjust the settings to allow for HTTPS traffic. Luckily, Nginx registers a few profiles with ufw upon installation.
You can see the current setting by typing: sudo ufw status
It will probably look like this, meaning that only HTTP traffic is allowed to the web server:
Status: active
To Action From
-- ------ ----
OpenSSH ALLOW Anywhere
Nginx HTTP ALLOW Anywhere
OpenSSH (v6) ALLOW Anywhere (v6)
Nginx HTTP (v6) ALLOW Anywhere (v6)
If not add it like so:sudo ufw allow 'Nginx HTTP'sudo ufw allow 'OpenSSH'
Reload the rules:sudo ufw reload
In case you need to delete a rule:sudo ufw delete allow 'Nginx HTTP'
Obtaining an SSL Certificate
Run this command to get a certificate and have Certbot edit your Nginx configuration automatically to serve it, turning on HTTPS access in a single step:
sudo certbot --nginx
If this is your first time running certbot, you will be prompted to enter an email address and agree to the terms of service. After doing so, certbot will communicate with the Let's Encrypt server, then run a challenge to verify that you control the domain you're requesting a certificate for.
If that's successful, certbot will ask how you'd like to configure your HTTPS settings.
Once you finish the setup. Your certificates are downloaded, installed, and loaded. Try reloading your website using https:// and notice your browser's security indicator. It should indicate that the site is properly secured, usually with a green lock icon. If you test your server using the SSL Labs Server Test, it will get an A grade.
Verifying Certbot Auto-Renewal
Let's Encrypt's certificates are only valid for ninety days. This is to encourage users to automate their certificate renewal process. The certbot package we installed takes care of this for us by adding a renew script to /etc/cron.d. This script runs twice a day and will automatically renew any certificate that's within thirty days of expiration.
To test the renewal process, you can do a dry run with certbot:sudo certbot renew --dry-run
If you see no errors, you're all set. When necessary, Certbot will renew your certificates and reload Nginx to pick up the changes. If the automated renewal process ever fails, Let’s Encrypt will send a message to the email you specified, warning you when your certificate is about to expire.
Their documentation
Problems that may arise:
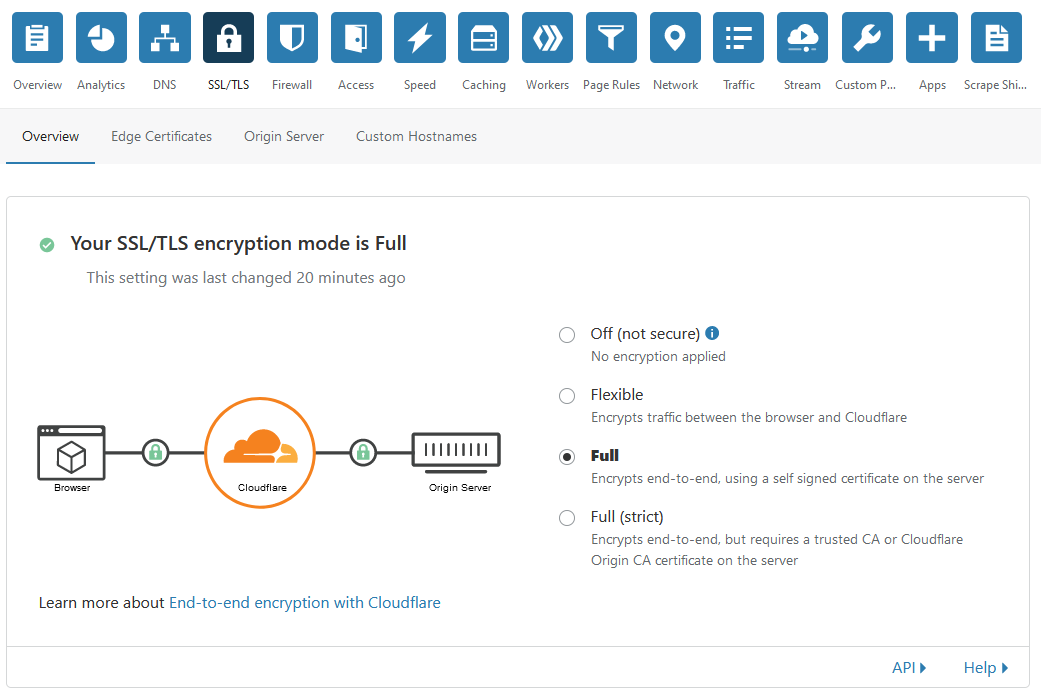
If your website is behind a CDN (like CloudFlare) or reverse proxy, make sure it looks like this:
What's next?
Check out this Index page